Email threats have evolved. Today, many of the most damaging incidents begin quietly, with a compromised mailbox and a message that looks completely legitimate. That’s where Managed Email Security proves its value. It does not read your emails. Instead, it helps detect and contain account takeovers before they escalate into costly business email compromise (BEC) attacks.
The Internet Crime Complaint Center (IC3), operated by the Federal Bureau of Investigation (FBI), reported that BEC was one of the costliest forms of cyber-enabled fraud in 2024, with 21,442 complaints and close to $2.8 billion in losses.
Separately, Barracuda’s Email Security Trends report noted that 75% of organizations experienced a successful email attack. These numbers highlight the need for proactive, privacy-respecting email protection.
Why Traditional Filters Aren’t Enough
Spam filters and antivirus tools are essential, but they are not built to stop sophisticated attacks that rely on trust and timing. Phishing emails and BEC scams often bypass these defenses by mimicking legitimate communication. Attackers may hijack real accounts, reply to existing threads, or impersonate executives to request payments or sensitive data.
Even with email authentication protocols such as Sender Policy Framework (SPF), DomainKeys Identified Mail (DKIM), and Domain-based Message Authentication, Reporting, and Conformance (DMARC), account takeovers remain a threat. These controls are part of the Cybersecurity and Infrastructure Security Agency (CISA) Binding Operational Directive 18-01 (BOD 18-01) guidance for enhancing email security, including SPF, DKIM, and DMARC. Once inside, attackers can operate from a trusted address, which makes their messages harder to detect.
Modern email security must go beyond content scanning. It should analyze sender behavior, detect anomalies, and flag unusual mailbox activity. Industry guidance commonly recommends layered approaches that combine anomaly detection with signals such as communication-pattern and writing-style analysis to help identify email fraud attempts. These layers help detect subtle threats without disrupting legitimate communication.
Security Without Compromising Privacy
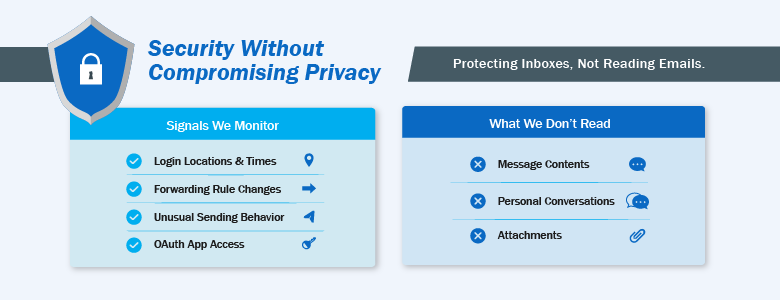
A common concern with managed email services is privacy. The term “monitoring” can raise red flags, especially among executives. But Managed Email Security is not about reading messages. It is about detecting risk signals.
These services focus on metadata such as login patterns, forwarding rules, and unusual sending behavior. They do not require reading message content to be effective. CISA’s guidance emphasizes strengthening email trust and authenticity through protocols and standards, not through human review of private email content.
A simple way to explain it is this: Managed Email Security keeps malicious emails out and flags early signs of compromise, without opening or reading employee emails. This clarity builds trust and improves adoption across the organization.
5 Signs of Account Takeover You Shouldn’t Ignore
Unexpected Forwarding Rules
One of the first things attackers do after compromising an account is create auto-forwarding rules. These silently send copies of emails, especially those containing keywords like “invoice” or “payment”, to external addresses. This allows attackers to monitor conversations and plan their next move.
These rules often go unnoticed by users. Managed Email Security can detect and flag new or suspicious forwarding rules, giving your team a chance to investigate before damage is done.
Hidden Filters or Deletion Rules
Attackers may create rules that delete or hide emails from specific senders, like the Chief Financial Officer (CFO) or the IT team, to avoid detection. These rules can persist even after a password reset or after multi-factor authentication (MFA) is enabled.
A managed service can detect when rules are created to move emails to obscure folders or trash, especially if they contain sensitive keywords. Early detection here can prevent attackers from manipulating conversations or hiding their tracks.
Suspicious OAuth App Access
Attackers increasingly use malicious Open Authorization (OAuth) applications to gain persistent access to email accounts. These apps can bypass MFA and remain active even after password changes because access tokens may stay valid until revoked.
Managed Email Security services that monitor OAuth grants and application permissions can detect and revoke unauthorized access before it’s exploited.
Unusual Login Patterns
Logins from unexpected locations or at odd hours, especially when followed by mailbox changes, are strong indicators of compromise. A 3:00 AM login from an unfamiliar Internet Protocol (IP) address followed by a new forwarding rule should trigger immediate investigation.
Managed services correlate login data with other signals to identify high-risk behavior and respond quickly. This can include escalating alerts or guiding containment steps.
Outbound Email Spikes
A sudden surge in outbound emails from a normally quiet account is a red flag. Attackers often use compromised accounts to send phishing emails or fraudulent requests to internal and external contacts.
Managed Email Security platforms baseline normal sending behavior and alert your team when something deviates significantly. This helps prevent reputational damage and stops attackers from spreading further.
Dark Web Exposure: What It Means and How to Respond
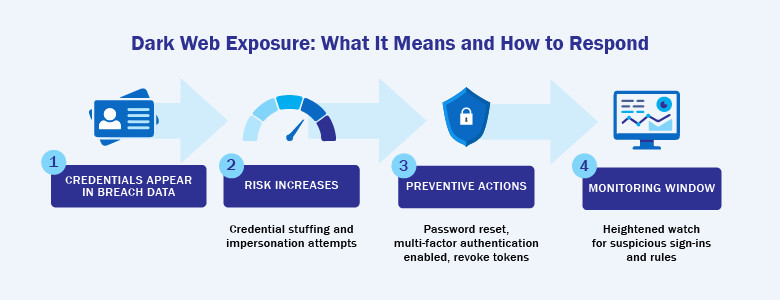
Dark web monitoring is now a common feature in many managed email security services. If an executive’s credentials appear in a breach dump, it does not automatically mean the mailbox is compromised. It does mean the risk just increased.
Treat exposures as urgent. Reset passwords, ensure MFA is enabled, and monitor the account closely. Communicate clearly with leadership: “We found credentials in a breach database. We’ve taken preventive steps, and there’s no evidence of misuse.”
Managed services can alert you quickly, which helps you act before attackers do.
How Managed Email Security Supports Your IT Team
For many IT teams, the challenge is not a lack of expertise. It is time and coverage. A managed service reduces alert fatigue by filtering noise and surfacing only the most relevant threats. It handles policy tuning, rule management, and ongoing monitoring so your team can stay focused on priorities that move the business forward.
You also get executive-ready reporting. Instead of raw logs, you’ll see summaries like: “24 malicious emails blocked, including 3 targeting Finance with fake invoices.” This builds trust with leadership and shows measurable value.
If you want broader coverage beyond email, it helps to connect email signals with endpoint, network, and cloud telemetry. That’s where a managed security operations function becomes a natural complement. CT Link’s Managed Security Operations Center (MSOC) is described as providing 24/7 monitoring, threat detection, and incident management, along with reporting and visibility. It’s a practical way to extend security operations without adding headcount, especially for teams that need after-hours coverage.
Interested in learning more about how we can better help you secure your business with MSOC? Contact us at marketing@ctlink.com.ph to set a meeting with us today!

